Security Operations Platform
One platform for detection, intelligence, and response
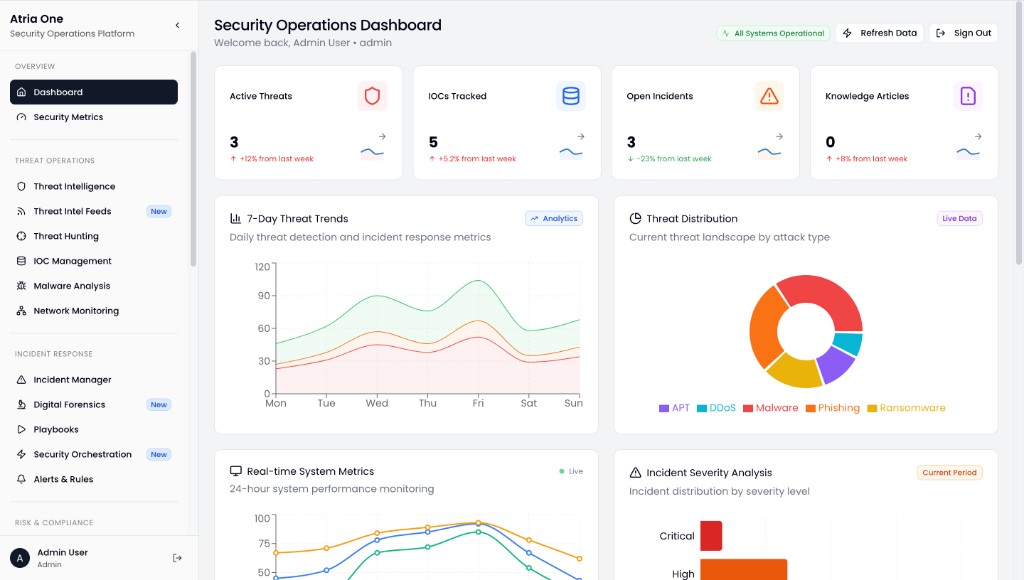
Atria One unifies threat operations, incident response, and risk insight in one workspace. Your team sees the full picture, moves faster, and stays aligned from the SOC to leadership.
Works with your existing stack—Splunk, IBM QRadar, ArcSight, MISP, ThreatConnect, and more. See integrations.
The operating layer
One workspace from alert to audit.
Posture and trends when stakeholders need the headline, and a defensible trail when you need to show what happened.
Visibility
Shared dashboards and severity so everyone in the room is looking at the same threat picture, not a slide deck from last week.
Depth
When summaries aren't enough, analysts stay in flow with hunting, IOCs, malware context, and network signals, without exporting to disconnected tools.
Closure
Playbooks, evidence, and reports that still make sense after the incident is closed, audit-ready without rebuilding the story from attachments and screenshots.
Capabilities
What the platform covers
Four domains in plain terms so you can map them to your org, tooling, and team structure, not ours.
- Threat operations
- Feeds, enrichment, hunting, and IOC lifecycle in one thread: prioritize signal, document context, and push action back to the tools that execute it.
- Incident response
- Cases, forensics handoffs, and playbooks aligned to your runbooks, so on-call isn’t reinventing steps at 2 a.m.
- Risk & compliance
- Assets, vulnerabilities, and control narratives in the same risk language leadership and auditors already expect.
- Analytics & reporting
- Scheduled and ad-hoc reporting that bridges the SOC and the boardroom without duplicate spreadsheets.
Workflow
End-to-end incident response
A simple spine you can map to your own tiers and tools. Atria One keeps one narrative from first alert through response to audit-ready closure.
-
1
Ingest & detect
Alerts and telemetry land from SIEM, EDR, and cloud, correlated into something humans can triage.
-
2
Enrich & decide
Intel feeds and IOC history answer “is this ours?” before you open a war room.
-
3
Respond & contain
Cases, playbooks, and orchestration hooks keep owners and timelines explicit.
-
4
Prove & improve
Metrics, knowledge base updates, and audit-friendly exports close the loop for compliance and retros.
Connects to tools you already own
Atria One is designed for enterprise glue: SIEM analytics, commercial and open intel, identity, and standard exchange formats, so rollout augments your stack instead of replacing it on day one.
SIEM & log analytics
- Splunk
- IBM QRadar
- Micro Focus ArcSight
Ingest and forward-friendly for centralized visibility.
Threat intelligence
- MISP
- ThreatConnect
- Anomali
Commercial feeds and sharing platforms alongside your own sources.
Identity & orchestration
- LDAP / Active Directory
- SOAR & ticketing platforms
- EDR & vulnerability scanners
Align users, cases, and automated actions with existing IT workflows.
Standards & transport
- STIX / TAXII
- REST APIs
- Syslog / CEF
- Webhooks
- CSV & JSON export
Meet security and compliance teams where their data contracts already live.
Built for enterprise expectations
Designed with controls mapping, audit trails, and reporting in mind, aligned to how teams talk about SOC 2, ISO 27001, NIST CSF, and GDPR-style data stewardship.
Book a guided walkthrough
Bring your use cases, and we’ll show the parts of Atria One that match your tiering, feeds, and stakeholders.
Contact sales
Tell us about your organization and what you’re looking to solve. Our team will follow up to schedule a conversation or live demo.
For general inquiries, you can also email hello@atriaone.com.